|
The iPhone Wiki is no longer updated. Visit this article on The Apple Wiki for current information. |
Difference between revisions of "Absinthe"
m |
(→Compatibility: use templates) |
||
| (16 intermediate revisions by 5 users not shown) | |||
| Line 1: | Line 1: | ||
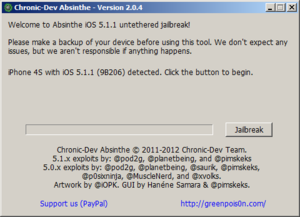
| + | [[File:Absinthe204win.png|thumb|right|Absinthe Version 2.0.4 on Windows]] |
||
| − | {{lowercase}} |
||
| + | '''Absinthe''' is the [[S5L8940|A5]] [[userland]] jailbreak tool for [[N94AP|iPhone 4S]] and [[iPad 2]] on iOS 5.0 (iPhone 4S only) and 5.0.1. This tool was released on {{date|2012|01|20}}, and is available in three incarnations: |
||
| − | [[File:Absinthe204win.png|thumb|right|absinthe Version 2.0.4 on Windows]] |
||
| − | '''absinthe''' is the [[S5L8940|A5]] [[userland jailbreak]] tool for [[n94ap|iPhone 4S]] and [[iPad 2]] on iOS 5.0 (iPhone 4S only), 5.0.1 (9A405) and [[Telluride 9A406 (iPhone 4S)|iOS 5.0.1 build 9A406]] on iPhone 4S. This tool was released on January 20, 2012, and is available in three incarnations: |
||
*A GUI tool with the same name, released by the [[Chronic Dev (team)|Chronic Dev Team]] |
*A GUI tool with the same name, released by the [[Chronic Dev (team)|Chronic Dev Team]] |
||
*A command-line version by the [[iPhone Dev Team]], in case troubleshooting is required |
*A command-line version by the [[iPhone Dev Team]], in case troubleshooting is required |
||
*An integration with [[redsn0w]] |
*An integration with [[redsn0w]] |
||
| − | + | Newer versions (2.0 - 2.0.4) supported all devices from iOS 5.0.1 and 5.1.1. This preinstalled [[Rocky Racoon]] from [[Cydia.app|Cydia]] to untether. |
|
| − | The name |
+ | The name Absinthe was chosen as an homage to [[greenpois0n]], Chronic Dev Team's earlier jailbreak software. [[wikipedia:Absinthe|Absinthe]] is an alcoholic beverage that is often greenish in color and is poisonous in quantity. |
== Installation == |
== Installation == |
||
| Line 15: | Line 14: | ||
==Exploit== |
==Exploit== |
||
{{main|Corona}} |
{{main|Corona}} |
||
| + | {{main|Rocky Racoon}} |
||
This jailbreak uses the [[Racoon String Format Overflow Exploit]] and [[HFS Heap Overflow]] from [[Corona]] for [[untethered jailbreak|untether]]. |
This jailbreak uses the [[Racoon String Format Overflow Exploit]] and [[HFS Heap Overflow]] from [[Corona]] for [[untethered jailbreak|untether]]. |
||
The exact exploit to jailbreak the two devices is not known yet, but it is assumed that the web clip loads a page that requires an IPsec VPN connection, which causes the [http://ipsec-tools.sourceforge.net racoon] daemon to start and run the jailbreak payload. |
The exact exploit to jailbreak the two devices is not known yet, but it is assumed that the web clip loads a page that requires an IPsec VPN connection, which causes the [http://ipsec-tools.sourceforge.net racoon] daemon to start and run the jailbreak payload. |
||
| Line 20: | Line 20: | ||
However, some poking reveals some unique means of injection. At some point in the jailbreak process, [[BackupAgent]] is intentionally crashed to produce a crash log. The jailbreak payload reads this crash log in order to obtain the memory address of libcopyfile.dylib to continue with the exploit. |
However, some poking reveals some unique means of injection. At some point in the jailbreak process, [[BackupAgent]] is intentionally crashed to produce a crash log. The jailbreak payload reads this crash log in order to obtain the memory address of libcopyfile.dylib to continue with the exploit. |
||
| − | Opening the <code>webclip_Info.plist</code> file included with the GUI tool, which is the definition file for the web clip, [http://cache.greenpois0n.com/abs0/index.html an URL to the greenpois0n website] is found, which shows a please wait message. The interesting part is the source code of this page has an image linked to <code>http://127.0.0.1/trigger.png</code>, because <code>127.0.0.1</code> was designated as the trigger site for a VPN on-demand configuration and any attempt at accessing a resource on <code>127.0.0.1</code> will trigger the VPN. Note that there is no actual web server running on <code>localhost</code>. |
+ | Opening the <code>webclip_Info.plist</code> file included with the GUI tool, which is the definition file for the web clip, [http://cache.greenpois0n.com/abs0/index.html an URL to the greenpois0n website][dead] is found, which shows a please wait message. The interesting part is the source code of this page has an image linked to <code>http://127.0.0.1/trigger.png</code>, because <code>127.0.0.1</code> was designated as the trigger site for a VPN on-demand configuration and any attempt at accessing a resource on <code>127.0.0.1</code> will trigger the VPN. Note that there is no actual web server running on <code>localhost</code>. |
| + | |||
| + | ==Compatibility== |
||
| + | |||
| + | {| class="wikitable" |
||
| + | |- |
||
| + | ! scope="col" | |
||
| + | ! scope="col" | 5.0 (9A334) |
||
| + | ! scope="col" | 5.0.1 (9A406) |
||
| + | ! scope="col" | 5.0.1 (9A405) |
||
| + | ! scope="col" | 5.1 (9B179) |
||
| + | ! scope="col" | 5.1 (9A405) |
||
| + | ! scope="col" | 5.1.1 (9B206) |
||
| + | ! scope="col" | 5.1.1 (9B208) |
||
| + | |- |
||
| + | ! scope="row" | [[N88AP|iPhone 3GS]] |
||
| + | | {{no}} |
||
| + | | {{yes}} |
||
| + | | {{n/a}} |
||
| + | | {{no}} |
||
| + | | {{n/a}} |
||
| + | | {{yes}} |
||
| + | | {{n/a}} |
||
| + | |- |
||
| + | ! scope="row" | [[N90AP|iPhone 4 (GSM)]] |
||
| + | | {{no}} |
||
| + | | {{yes}} |
||
| + | | {{n/a}} |
||
| + | | {{no}} |
||
| + | | {{n/a}} |
||
| + | | {{yes}} |
||
| + | | {{yes}} |
||
| + | |- |
||
| + | ! scope="row" | [[N92AP|iPhone 4 (CDMA)]] |
||
| + | | {{no}} |
||
| + | | {{yes}} |
||
| + | | {{n/a}} |
||
| + | | {{no}} |
||
| + | | {{n/a}} |
||
| + | | {{yes}} |
||
| + | | {{n/a}} |
||
| + | |- |
||
| + | ! scope="row" | [[N94AP|iPhone 4S]] |
||
| + | | {{yes}} |
||
| + | | {{yes}} |
||
| + | | {{yes}} |
||
| + | | {{no}} |
||
| + | | {{no}} |
||
| + | | {{yes}} |
||
| + | | {{n/a}} |
||
| + | |- |
||
| + | ! scope="row" | [[K48AP|iPad]] |
||
| + | | {{no}} |
||
| + | | {{yes}} |
||
| + | | {{n/a}} |
||
| + | | {{no}} |
||
| + | | {{n/a}} |
||
| + | | {{yes}} |
||
| + | | {{n/a}} |
||
| + | |- |
||
| + | ! scope="row" | [[K93AP|iPad 2 Wi-Fi]] |
||
| + | | {{no}} |
||
| + | | {{yes}} |
||
| + | | {{n/a}} |
||
| + | | {{no}} |
||
| + | | {{n/a}} |
||
| + | | {{yes}} |
||
| + | | {{n/a}} |
||
| + | |- |
||
| + | ! scope="row" | [[K94AP|iPad 2 Wi-Fi + 3G (GSM)]] |
||
| + | | {{no}} |
||
| + | | {{yes}} |
||
| + | | {{n/a}} |
||
| + | | {{no}} |
||
| + | | {{n/a}} |
||
| + | | {{yes}} |
||
| + | | {{n/a}} |
||
| + | |- |
||
| + | ! scope="row" | [[K95AP|iPad 2 Wi-Fi + 3G (CDMA]] |
||
| + | | {{no}} |
||
| + | | {{yes}} |
||
| + | | {{n/a}} |
||
| + | | {{no}} |
||
| + | | {{n/a}} |
||
| + | | {{yes}} |
||
| + | | {{n/a}} |
||
| + | |- |
||
| + | ! scope="row" | [[K93AAP|iPad 2 Wi-Fi (Mid 2012)]] |
||
| + | | {{n/a}} |
||
| + | | {{n/a}} |
||
| + | | {{n/a}} |
||
| + | | {{no}} |
||
| + | | {{n/a}} |
||
| + | | {{yes}} |
||
| + | | {{n/a}} |
||
| + | |- |
||
| + | ! scope="row" | [[J1AP|iPad (3rd generation) Wi-Fi]] |
||
| + | | {{no}} |
||
| + | | {{yes}} |
||
| + | | {{n/a}} |
||
| + | | {{no}} |
||
| + | | {{n/a}} |
||
| + | | {{yes}} |
||
| + | | {{n/a}} |
||
| + | |- |
||
| + | ! scope="row" | [[J2AP|iPad (3rd generation) Wi-Fi + Cellular (VZ)]] |
||
| + | | {{no}} |
||
| + | | {{yes}} |
||
| + | | {{n/a}} |
||
| + | | {{no}} |
||
| + | | {{n/a}} |
||
| + | | {{yes}} |
||
| + | | {{n/a}} |
||
| + | |- |
||
| + | ! scope="row" | [[J2AAP|iPad (3rd generation) Wi-Fi + Cellular]] |
||
| + | | {{no}} |
||
| + | | {{yes}} |
||
| + | | {{n/a}} |
||
| + | | {{no}} |
||
| + | | {{n/a}} |
||
| + | | {{yes}} |
||
| + | | {{n/a}} |
||
| + | |- |
||
| + | ! scope="row" | [[N18AP|iPod touch (3rd generation)]] |
||
| + | | {{no}} |
||
| + | | {{yes}} |
||
| + | | {{n/a}} |
||
| + | | {{no}} |
||
| + | | {{n/a}} |
||
| + | | {{yes}} |
||
| + | | {{n/a}} |
||
| + | |- |
||
| + | ! scope="row" | [[N81AP|iPod touch (4th generation)]] |
||
| + | | {{no}} |
||
| + | | {{yes}} |
||
| + | | {{n/a}} |
||
| + | | {{no}} |
||
| + | | {{n/a}} |
||
| + | | {{yes}} |
||
| + | | {{n/a}} |
||
| + | |} |
||
[[Category:Hacking Software]] |
[[Category:Hacking Software]] |
||
[[Category:Jailbreaks]] |
[[Category:Jailbreaks]] |
||
| + | [[Category:Jailbreaking]] |
||
Latest revision as of 13:30, 8 December 2021
Absinthe is the A5 userland jailbreak tool for iPhone 4S and iPad 2 on iOS 5.0 (iPhone 4S only) and 5.0.1. This tool was released on 20 January 2012, and is available in three incarnations:
- A GUI tool with the same name, released by the Chronic Dev Team
- A command-line version by the iPhone Dev Team, in case troubleshooting is required
- An integration with redsn0w
Newer versions (2.0 - 2.0.4) supported all devices from iOS 5.0.1 and 5.1.1. This preinstalled Rocky Racoon from Cydia to untether.
The name Absinthe was chosen as an homage to greenpois0n, Chronic Dev Team's earlier jailbreak software. Absinthe is an alcoholic beverage that is often greenish in color and is poisonous in quantity.
Installation
The jailbreak packs Corona for the S5L8940 and the rest of the firmware patches in a regular iTunes backup and then restores this backup on to the device, which injects the required files. It is then completed by opening a web clip added to the home screen by Absinthe. If this doesn't work, for example, because the greenpois0n website is down due to the number of people attempting to jailbreak, an alternative is to enable a specially crafted VPN connection in the Settings app.
Exploit
- Main article: Corona
- Main article: Rocky Racoon
This jailbreak uses the Racoon String Format Overflow Exploit and HFS Heap Overflow from Corona for untether. The exact exploit to jailbreak the two devices is not known yet, but it is assumed that the web clip loads a page that requires an IPsec VPN connection, which causes the racoon daemon to start and run the jailbreak payload.
However, some poking reveals some unique means of injection. At some point in the jailbreak process, BackupAgent is intentionally crashed to produce a crash log. The jailbreak payload reads this crash log in order to obtain the memory address of libcopyfile.dylib to continue with the exploit.
Opening the webclip_Info.plist file included with the GUI tool, which is the definition file for the web clip, an URL to the greenpois0n website[dead] is found, which shows a please wait message. The interesting part is the source code of this page has an image linked to http://127.0.0.1/trigger.png, because 127.0.0.1 was designated as the trigger site for a VPN on-demand configuration and any attempt at accessing a resource on 127.0.0.1 will trigger the VPN. Note that there is no actual web server running on localhost.
Compatibility
| 5.0 (9A334) | 5.0.1 (9A406) | 5.0.1 (9A405) | 5.1 (9B179) | 5.1 (9A405) | 5.1.1 (9B206) | 5.1.1 (9B208) | |
|---|---|---|---|---|---|---|---|
| iPhone 3GS | No | Yes | N/A | No | N/A | Yes | N/A |
| iPhone 4 (GSM) | No | Yes | N/A | No | N/A | Yes | Yes |
| iPhone 4 (CDMA) | No | Yes | N/A | No | N/A | Yes | N/A |
| iPhone 4S | Yes | Yes | Yes | No | No | Yes | N/A |
| iPad | No | Yes | N/A | No | N/A | Yes | N/A |
| iPad 2 Wi-Fi | No | Yes | N/A | No | N/A | Yes | N/A |
| iPad 2 Wi-Fi + 3G (GSM) | No | Yes | N/A | No | N/A | Yes | N/A |
| iPad 2 Wi-Fi + 3G (CDMA | No | Yes | N/A | No | N/A | Yes | N/A |
| iPad 2 Wi-Fi (Mid 2012) | N/A | N/A | N/A | No | N/A | Yes | N/A |
| iPad (3rd generation) Wi-Fi | No | Yes | N/A | No | N/A | Yes | N/A |
| iPad (3rd generation) Wi-Fi + Cellular (VZ) | No | Yes | N/A | No | N/A | Yes | N/A |
| iPad (3rd generation) Wi-Fi + Cellular | No | Yes | N/A | No | N/A | Yes | N/A |
| iPod touch (3rd generation) | No | Yes | N/A | No | N/A | Yes | N/A |
| iPod touch (4th generation) | No | Yes | N/A | No | N/A | Yes | N/A |