|
The iPhone Wiki is no longer updated. Visit this article on The Apple Wiki for current information. |
PurpleSNIFF
This article discusses software internally used by Apple. Acquiring a copy without Apple's consent is illegal and may result in being scammed. |
 | |
|---|---|
| Original author(s) | Apple Inc. |
| Developer(s) | Apple Inc. |
| Stable release |
2.0 (83) (latest known version) |
| Operating system | macOS |
| Size | 53.9 MB |
| Available in | English |
| License | Closed source |
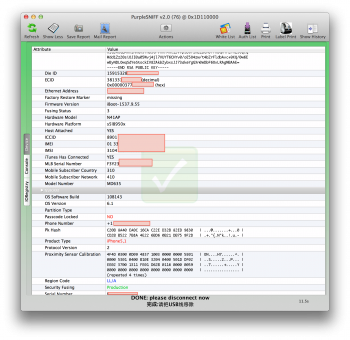
PurpleSNIFF is a tool made by Apple to read identification and diagnostic information from the device. The tool is used by Apple engineers as well as factory workers at Foxconn/Pegatron. It's included in the RestoreTools or Home Diagnostics package.
Like iTunes, PurpleSNIFF communicates with iDevices using a usbmux connection.
Device Information
PurpleSNIFF displays the value of all keys accessible by liblockdown and mobilegestaltd. Data is broken into categories:
- SNIFF: Report date and host machine configuration
- Battery: Battery charge state
- Debug: Lockdown and CLTM (thermal) extended logging.
- Developer: "Development" if has installed XCode developer diskimage.
- Device Mode: "OS Mode", "Recovery", "DFU", and possibly other internal modes.
- Diagnostic Data: Includes device test data from different factory stations, including their timestamps. There are over 300 testing stations devices can be tested on. Each device will usually pass through about 6 testing stations before shipping. The diagnostic platform is called iPCB.
- Disk Usage: Stats for both System and Data partitions
- General: Activation info, baseband identifiers and state, current carrier bundle, device certificate, public key, name, device color, ECID, MAC addresses, UDID, Serial Number, Hardware Model, Fusing Status, platform, architecture, IMEI/IMSI/ICCID, NVRAM data, OS Build/Version, passcode lock-state, proximity sensor calibration, region code, Security Fusing (secure or insecure), Production Mode (Production or Development), SIM card status, presence of Springboard/lockdown, and many more.
- Internal: isInternal and isCarrierBuild, isUIBuild, raw hex dump of SysCfg and DIAGS blocks.
- Localization: Language
- Mobile iTunes: Fairplay related parameters (e.g. certificate)
- Restore From Backup: If it has been restored from a backup
- Setup Assistant: YES/NO listing of which screens have been presented.
- Software Behavior: A bitmask that is decoded into the following boolean properties: China Brick, Google Mail, No VOIP, No Wi Fi, NTSC, Shutter Click, Valid, and Volume Limit.
- Sync: Device support for clearing data and encrypted backups, as well as mail accounts connected.
- Sync Backup: iCloud sync information.
- SysCfg: Device hardware information such as sensor calibration data, device color, NAND size, and serial numbers. This block is read-write for AppleInternal tool that must run on the device, so that Apple can refurbish devices and give them a new serial number.
- Wireless: Bonjour service name, Wifi support, Wifi-sync support.
White List
"Request White List Authorization" composes a new email to whitelist-request@group.apple.com. This email address is only reachable if you have an @apple.com email account. The address does not accept outside (external) senders. This feature allows a factory worker or Apple engineer to request that the device be SIM-unlocked for use on certain carriers.
TO: whitelist-request@group.apple.com SUBJECT: White-list Request Please whitelist the following device device: n41ap-prodfuse imei: 00...[redacted]...0 carriers: justification:
Auth List
"Request Personalized Install Authorization" composes a new email to authlist-request@group.apple.com. As with White List, this email address is only reachable if you have an @apple.com email account. This feature allows a factory worker or Apple engineer to request special firmware personalization for their device. This is useful because Apple could order prototypes of unreleased iPhones but refuse to sign any firmware for them. This way, if the devices are lost/leaked into the wild for some reason, the device is bricked. When prototype phones arrive safely/securely to Cupertino, engineers can have them activated for firmware personalization through this mechanism. It is not known the requests are to permit firmware signing on the public or internal (VPN-only) TSS server.
TO: authlist-request@group.apple.com SUBJECT: Authorization List Request Please authorize the following device device: n41ap-prodfuse ecid: 0[redacted]0 bbsn: 0x0[redacted]0 audience: restore tool: justification:
Extras
The other main tabs of the application reveal the live Syslog and the IORegistry hierarchy. Menu options include commands to enable extra logging, reboot devices (with optional prompt), obliterate and reset them, read diagnostic data from GasGauge, WIFI, and NAND, query MobileGestalt directly, enter and exit recovery, and "Lookup Device" in PDCA. It can also pull logs off of the device, as well as content in var/mobile/library . The log archive can be huge because it includes data like the SMS database and all MMS attachments).
PurpleSNIFF also tracks location, maybe for some sort of monitoring where and how the tool is used. Be careful with this, it may land you in trouble.
Trivia
- The waiting.wav track that plays while PurpleSNIFF is gathering information from your device is "Lan Ting Xu" by Jay Chou & Chi Ling Lin. The exact recording seems to be the one found here.